Infiltrating iPhones to Steal Cryptocurrency! The Attack Suite "Coruna" Ravages, Old iOS Versions at Risk of Being Lambs
Author: Max, Crypto City
Evolving from a national surveillance tool to an “asset harvesting machine”
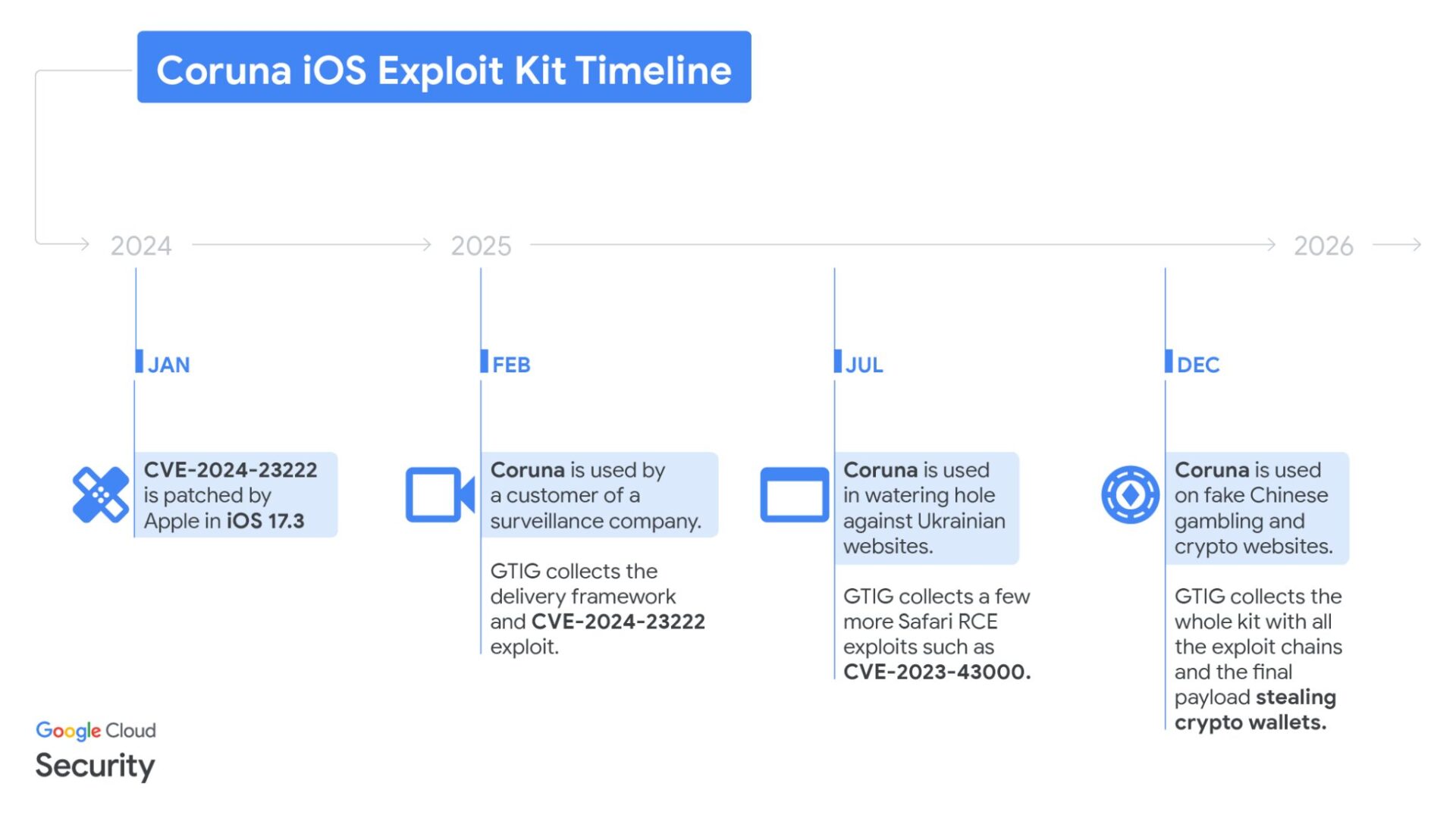
According to an in-depth report released by Google Threat Intelligence Group (GTIG), the iOS vulnerability suite codenamed Coruna (also known as CryptoWaters) poses a serious threat to users worldwide. The development of this tool has a highly dramatic trajectory. When first discovered in February 2025, it was provided by private surveillance vendors to government clients for targeted monitoring of politicians and dissenters. Later, in summer 2025, a hacker group linked to the Russian government, UNC6353, took control of the suite and used it for geopolitical espionage against Ukrainian citizens.
Image source: Google | Coruna Timeline
As the technology proliferated, this professionally developed tool, costing millions of dollars, has officially entered the cybercrime market. By late 2025 to early 2026, a Chinese hacker group, UNC6691, acquired the technology and shifted their attack focus to digital asset theft. This marks the commodification of high-level espionage tools, transforming from targeted intelligence gathering to large-scale theft of cryptocurrency holdings. Researchers note that hackers are willing to invest significant technical resources, indicating that the enormous profits behind crypto assets drive professional techniques into financial crime.
23 Vulnerabilities Chain Reaction: Silent Penetration Behind the “Watering Hole”
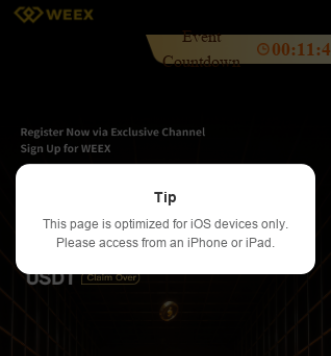
Coruna features a high degree of automation and stealth, integrating 23 independent vulnerabilities that form five complete attack chains. Its scope is extensive, affecting all iPhones and iPads running iOS 13.0 through iOS 17.2.1. The hackers employ a covert “watering hole attack,” infiltrating or setting up fake cryptocurrency exchanges and financial websites to lure victims. These sites, such as the counterfeit WEEX exchange, look and function almost identically to the real ones, even using SEO and paid ads to increase visibility.
Image source: Google | Fake WEEX Exchange
When iPhone users visit these compromised sites, background scripts immediately execute device recognition. The system silently checks the iOS version, and if the device falls within the targeted range, it automatically triggers zero-click (Zero-click) exploits, fully automated without any user interaction or clicking links. Some fake sites even proactively prompt users to browse with iOS devices, claiming better experience, but in reality, they are precisely targeting vulnerable devices that haven’t been updated.
Even screenshots in photo albums are not safe
Once Coruna successfully gains device access, its malicious component PlasmaLoader activates, conducting a scan of the user’s digital assets. This program has powerful scanning capabilities, actively searching for keywords like “backup phrase,” “bank account,” or “seed phrase,” and extracting key data from SMS and notes. It also features image recognition, automatically scanning screenshots in the user’s photo albums for QR codes containing wallet seed phrases or private keys.
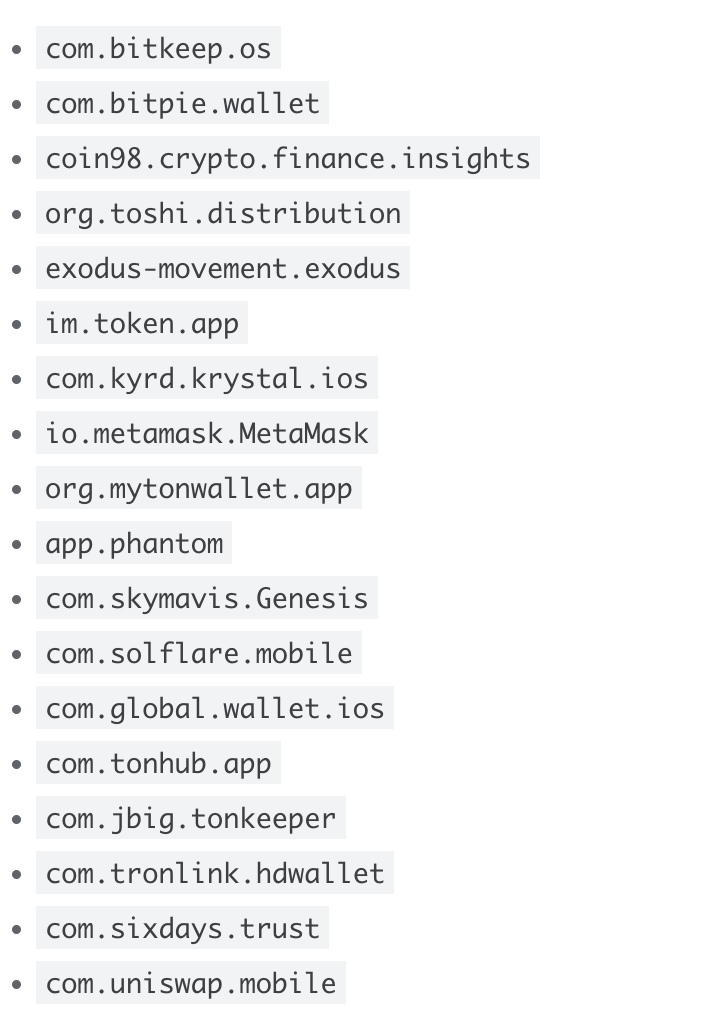
In addition to static data collection, Coruna targets mainstream crypto wallet apps like MetaMask and Uniswap. Hackers attempt to extract sensitive information from these apps to gain full control of wallets. In multiple known cases, victims’ funds were transferred shortly after visiting fake websites. Because the attack targets system-level permissions, any digital traces of private keys left on the device are difficult to escape from this espionage-grade tool.
Image source: Google | Google lists all apps potentially vulnerable to malicious attacks
Defense Rules and Survival Tips? System Updates Are Key to Security
In the face of sophisticated high-level threats, iPhone users should adopt clear protective measures. Google’s report states that Coruna is completely ineffective against iOS 17.3 or higher. Although newer system versions are available, some users still run outdated devices or lack space to update, exposing themselves to risk. For older models that cannot upgrade to secure versions, enabling Apple’s “Lockdown Mode” is an effective countermeasure. Once malicious software detects this mode, it will cease operation to avoid detection.
Cybersecurity experts recommend that crypto holders follow basic survival rules. The primary protection is to use hardware wallets (such as Ledger or Trezor), keeping private keys offline and disconnected from iOS environments. Additionally, all screenshots containing seed phrases or private keys should be immediately deleted from photo albums, and offline physical backups should be used instead.
Although Coruna avoids detection by steering clear of incognito browsing modes, this is only a temporary measure. As the value of digital assets continues to rise, maintaining software updates and cybersecurity vigilance has become a fundamental responsibility for every investor.
Related Articles
Polymarket reviews and weeds out early-stage projects in its ecosystem, targeting insider trading and market manipulation behaviors
In Q1 2026, Web3 projects suffered losses of over $460 million from hacks and scams, with phishing attacks leading the way.
RAVE’s hype surge triggers a flood of copycat coin mania, as FF and INX expose the “pump-and-dump” scheme
FBI teams up with Indonesia to dismantle W3LL phishing network, with more than $20 million involved
Squads Emergency Alert: Address poisoning and forged multisig accounts; a whitelist mechanism will go live
South Korean “retaliation intermediary” agencies charged USDT to carry out violent crimes, and continued operating even after the main suspect was arrested