Resolv Labs contract upgrade, forcibly destroys 36.73 million hacker USR tokens

The encryption protocol Resolv Labs upgraded via a smart contract on April 6, forcibly burning the 36.73 million USR stablecoins held in the attacker’s address. This is the latest progress in the response following the March 22 coin-minting vulnerability attack. The attacker used the leaked private key from the off-chain AWS key management service to mint 80 million unsecured USR with an initial collateral of less than $200k.
Attack Recap: How the Leaked AWS Key Triggered Systemic Losses
According to Chainalysis analysis, the core entry point of this attack was a leaked AWS KMS (Key Management Service) private key in Resolv’s off-chain authorization infrastructure. The attacker used this key to bypass the minting authorization mechanism and complete two main minting transactions on-chain: 50 million USR and 30 million USR, with initial collateral of only $100k to $200k in USDC.
The Attacker’s Funds Conversion Path
Minting: Mint 80 million unsecured USR with collateral of less than $200k
Conversion: Wrap USR into wstUSR (wrapped, collateralized version), and gradually exchange it for other stablecoins
Cash-Out: Ultimately convert to about 11,409 ETH, worth about $24.48 million
Price Impact: A large amount of unsecured tokens flooded DeFi liquidity pools, and USR briefly crashed to $0.14
Chainalysis noted that the fundamental flaw of this attack was that Resolv’s minting system lacked on-chain minting caps and on-chain verification mechanisms, relying entirely on off-chain signatures for authorization. Once the private key was leaked, it created a systemic exposure.
Resolv Labs’ Response: Contract Upgrade and Confirmation of the Loss Boundary
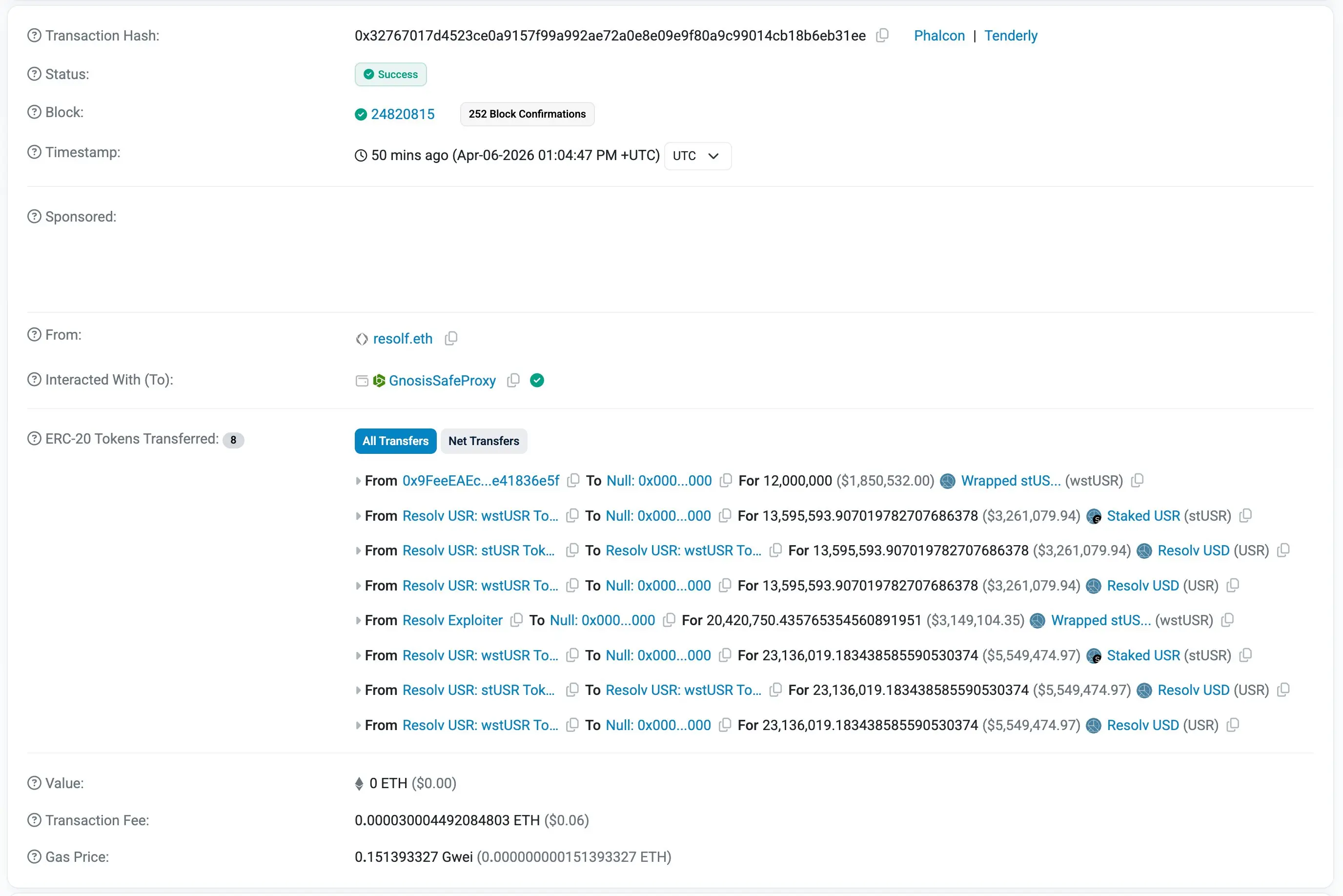 (Source: Etherscan)
(Source: Etherscan)
On April 6, on-chain analyst Yu Jin observed that Resolv Labs upgraded its contract to forcibly burn 36.73 million USR from the attacker’s address. Combined with earlier remediation actions, the Resolv team removed about 46 million USR from the attacker’s address through multiple contract upgrades.
However, some of the unsecured tokens that the attacker had already extracted in the form of ETH could not be recovered. The protocol ultimately confirmed the actual economic loss to be about $34 million. Resolv Labs emphasized that although the vulnerability led to the over-minting of 80 million USR, the protocol’s collateral pool “remains intact.”
This incident also highlights the duality of privileged contract control mechanisms—exactly the same upgrade authority can be used by attackers to trigger a crisis, or by the protocol to implement emergency damage control. For DeFi protocols that nominally advocate decentralization, this characteristic constitutes a long-term governance risk.
DeFi Security Alert: Off-Chain Infrastructure Is the Next Major Attack Surface
Even though Resolv passed 18 security audits, protection gaps in its off-chain AWS infrastructure still caused large-scale losses, underscoring the structural blind spots in the current scope of DeFi security audits.
Security researchers pointed out that if real-time on-chain monitoring tools such as Hexagate had been deployed, abnormal minting ratios could have been automatically flagged and contract execution paused early on, significantly reducing the scale of losses. The core takeaway from this incident is that a DeFi protocol’s security framework must include protections of equal priority to smart contract audits: backend key rotation mechanisms, cloud infrastructure access controls, and automatic circuit-breaker mechanisms for abnormal transactions.
Frequently Asked Questions
How did Resolv Labs forcibly burn the USR held by the hacker?
Resolv Labs performed a forced token burn operation on the attacker’s address through a smart contract upgrade mechanism. This action relies on the protocol’s privileged administrator permissions, allowing it to be executed on-chain without the attacker’s consent—enabling centralized emergency response measures.
What was the actual loss amount of this Resolv vulnerability?
The attacker already exchanged about 34 million USR for 11,409 ETH (about $24.48 million) and transferred it; this portion cannot be recovered. The protocol confirmed the actual net loss to be about $34 million. The 36.73 million USR that Resolv Labs burned were the remaining positions the attacker had not yet cashed out.
What impact did this attack have on the USR peg mechanism?
After the attack, USR briefly plunged to $0.14. It then gradually recovered after trading in the $0.23 to $0.27 range. Resolv Labs stated that the collateral pool was intact, but this incident already caused a structural blow to market confidence in the USR peg, and it prompted the protocol to pause operations and roll out a recovery plan.